Practical attackers exploit predictable interactions in AI agents to change their goals, leak data, or trigger dangerous actions. This article surveys five real-world hacks against AI agents and shows how common architectural choices open those paths. It highlights measurable defenses that reduce risk, why trade-offs between safety and usefulness exist, and which engineering steps give immediate protection for systems that use AI agents.
Introduction
Many practical systems now combine large language models with tools such as web fetchers, file readers, and small programs. That combination is useful because it lets an agent gather facts, run calculations, and act on behalf of a user. The cost is that each extra capability also becomes a new door an attacker can nudge open.
Consider a travel assistant that can read a user’s email and book tickets: the same code that lets the assistant open a calendar can be tricked into revealing parts of a message or invoking an API it should not. Those tricks are not just theoretical; recent benchmarks and incident studies show measurable success rates when attackers target multi-step, tool-enabled systems.
This article explains the core mechanics behind five common hacks, describes practical countermeasures that reduce measurable risk, and points to durable engineering patterns for teams running AI agents. The focus is on structural fixes that remain useful as models change.
How AI agents are built and where attacks enter
At a simple level, an AI agent is a control loop: a model receives a prompt, the system may fetch external data or call tools, the model produces an action or text, and the system executes or returns the result. Each step in that loop handles context, state, and permissions; each is a potential attack surface.
Two structural design choices explain most vulnerabilities. First, blending trusted system prompts with untrusted, external content can let a crafted input override prior instructions. Second, giving the agent live access to tools or data stores means an attacker who controls or influences any retrieved content can induce harmful outputs or extract sensitive information.
“Treat model outputs and external content as untrusted by default.”
Below is a compact view of common points of weakness and what an attacker typically gains.
| Feature | Description | Typical impact |
|---|---|---|
| Mixed context | System instructions concatenated with web-retrieved text | Instruction override, task hijack |
| Tool access | Agent can call APIs, run code, or read files | Data exfiltration, unauthorized actions |
| Embedding/index use | RAG (retrieval-augmented generation) pulls unvetted documents | Leakage of sensitive fields |
Research that measures real attacks on multi-step agents finds that success rates vary by task and model but are non-negligible when external content is present. The practical takeaway is straightforward: control how external content enters the loop, and assume any output must be validated before use.
Five real-world hacks that compromise AI agents
These five hacks are repeatedly seen in academic benchmarks and security reviews of tool-enabled agents. For each, the explanation is short and the mitigation is concrete so teams can act quickly.
1. Prompt injection via retrieved documents
What it is: When an agent uses retrieval to add external text to a prompt, an attacker who controls or poisons those documents can insert instructions that the model follows. This can change the agent’s behaviour or cause it to reveal data saved in context.
How to block it: Segregate untrusted text with explicit delimiters, send it in a separate channel marked “untrusted”, and run a prompt-injection detector before any retrieval content is allowed into the reasoning context. For highly sensitive tasks, require a human confirmation step before actions based on retrieved content are executed.
2. Tool-output manipulation and plugin abuse
What it is: Many agents call plugins or tools (e.g., web browsers, calculators). If a plugin returns attacker-crafted text, the agent can follow malicious instructions or leak secrets during subsequent steps.
How to block it: Use least-privilege for plugins, validate and sanitize every tool output, and isolate tools so they cannot access credentials or persistent state unless strictly necessary. Maintain allowlists for trusted plugins and rate-limit new plugin installation.
3. Exfiltration through multi-step reasoning
What it is: Agents that iteratively gather facts and refine answers can be coaxed to reveal sensitive fields by asking for summaries or for related-but-unexpected outputs. Attackers combine low-sensitivity and high-sensitivity cues to make the model surface hidden data.
How to block it: Track data provenance during each step, tag retrieved facts with sensitivity labels, and refuse to use or return high-sensitivity items unless explicit, auditable authorization exists. Logging each retrieval and redaction before output is crucial for forensics.
4. Credential and environment leakage
What it is: Hard-coded keys, overly broad API tokens, or environment variables accessible to the agent create a direct route to secrets. If the agent can compose a request that includes those secrets, an attacker can extract them.
How to block it: Remove secrets from model-accessible scopes, use short-lived tokens, and implement strict Role-Based Access Controls for any API the agent can reach. Test with simulated exfiltration attempts to ensure tokens can’t be reconstructed from outputs.
5. Multimodal and obfuscated payloads
What it is: Attackers increasingly hide instructions in images, code blocks, or obfuscated math expressions that evade simple text filters. When agents process multimodal inputs, they may follow hidden directives embedded in non-textual content.
How to block it: Treat all non-textual inputs as potentially hostile, run modality-specific detectors (image OCR checks, code parsers), and avoid automatic execution of code or transformations without human review. Where possible, restrict the types of files an agent may open.
Those five hacks explain most successful attacks measured in recent agent benchmarks: they exploit mixed contexts, tool access, and insufficient isolation between trusted and untrusted material. The engineering answers are layered: prevent, detect, and contain.
What these attacks mean for everyday use
For consumers, the risk looks like unusual behaviour in a familiar assistant: wrong recommendations, surprising disclosures, or unapproved actions such as sending a message. For companies, the stakes include data breaches and compliance failures. In practice, the severity depends on how much power an agent has and what safeguards surround it.
Benchmarks give a helpful calibration: measured success rates for indirect prompt-injection and related attacks vary, but modern studies find non-zero rates when agents retrieve external data. Defences that combine input sanitation, an ML-based injection detector, and tool isolation can reduce those rates dramatically, sometimes to near zero in controlled tests—but usually at a cost to convenience or completeness.
The trade-off is concrete. For example, forcing a human to approve any action that touches personal data removes a large class of attacks, yet it slows workflows and raises operational cost. Similarly, aggressive sanitization can strip useful context from retrieved documents, reducing answer quality. Security teams therefore need to measure both safety gains and utility losses.
A practical pattern that balances the two is defense-in-depth: make small, low-cost changes first (strict token scopes, delimit untrusted text, log actions), add automated detectors and redaction for frequent tasks, and reserve human review for high-impact operations. Continuous red‑teaming—regularly running adversarial prompts against your agent—helps keep the balance calibrated as models and attack techniques evolve.
Where defenses are heading
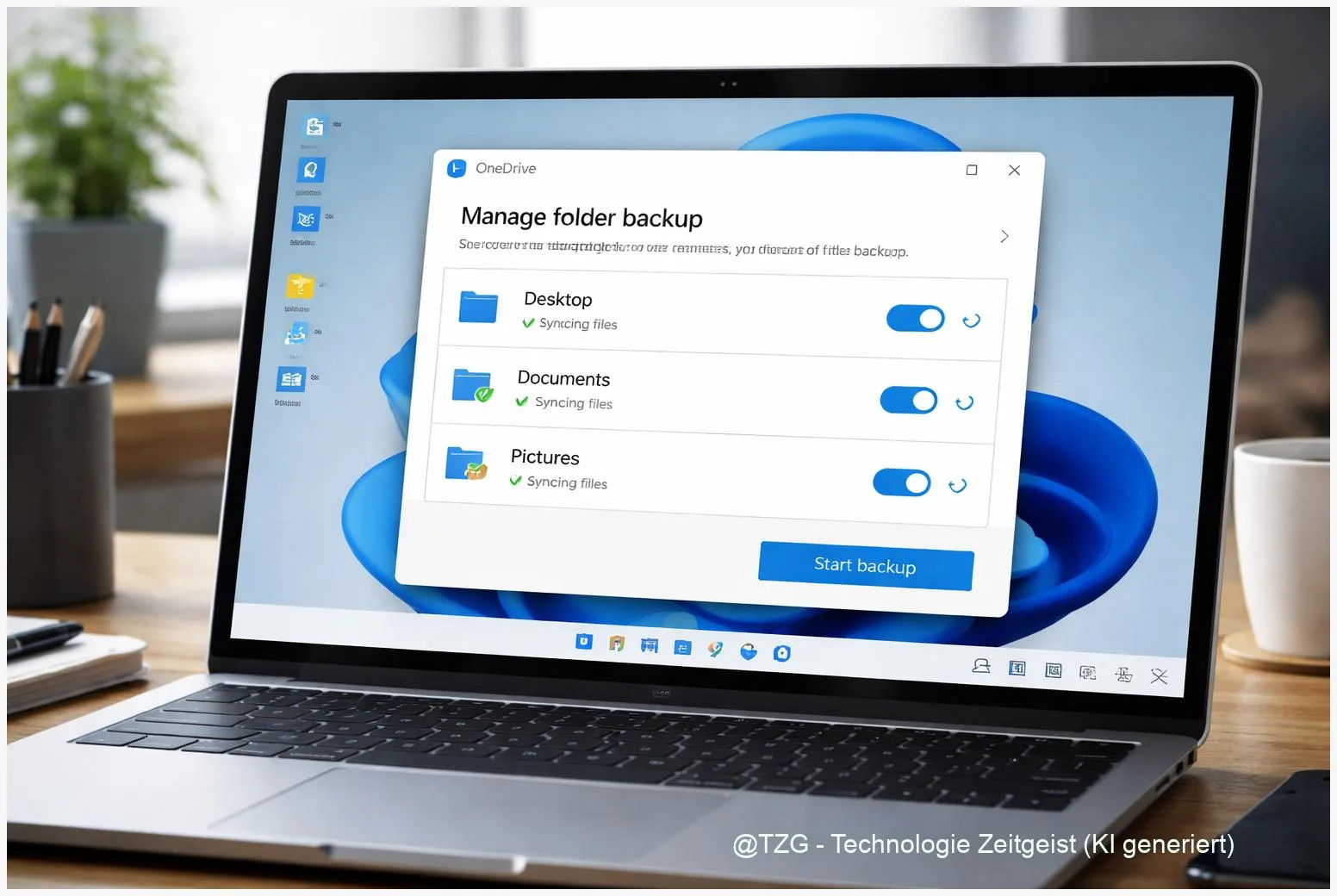
Defensive work has moved beyond simple blacklists. Leading recommendations now treat agent security as a data-flow problem: map each input to an origin, mark it as trusted or not, and ensure that only explicitly allowed data flows reach sensitive actions. Community frameworks such as the OWASP LLM Top Ten and recent agent benchmarks push this pattern.
Two technical trends deserve attention. First, detectors that combine heuristic checks with small specialist models are becoming standard; they flag likely injection payloads before the main model sees them. Second, tool isolation and least-privilege are increasingly enforced by runtime sandboxes that hold tokens and only grant ephemeral access under strict checks.
Looking forward, teams should introduce several durable controls: a data-flow-aware threat model for every agent deployment; continuous adversarial testing that includes gradient-based and multimodal attacks; and auditable, red-team driven benchmarks that measure both security (for example, reduced leakage rates) and utility (accuracy, speed).
For operators and managers, prioritize fixes that are cheap to implement and high impact: narrow API scopes, separate untrusted content, require human approval for critical actions, and log every retrieval. Over time, adopt standard benchmarks and vendor assessments so new components enter production only after adversarial evaluation.
Conclusion
AI agents offer practical benefits but also concentrate new security risks where models, tools, and external data meet. The five real-world hacks described here—prompt injection via retrieval, plugin abuse, iterative exfiltration, credential leakage, and multimodal obfuscation—share a common root: unchecked data flow and excessive privileges. Practical protection is available today and relies on layered measures: mark and separate untrusted inputs, limit tool privileges, run detectors before the model ingests external content, and require human review for sensitive actions. Those steps reduce measurable leakage while keeping many agent benefits.
If you run or build AI agents, share this article with a colleague and describe one control you could add this week.

Leave a Reply